The Shadow AI Crisis in Numbers
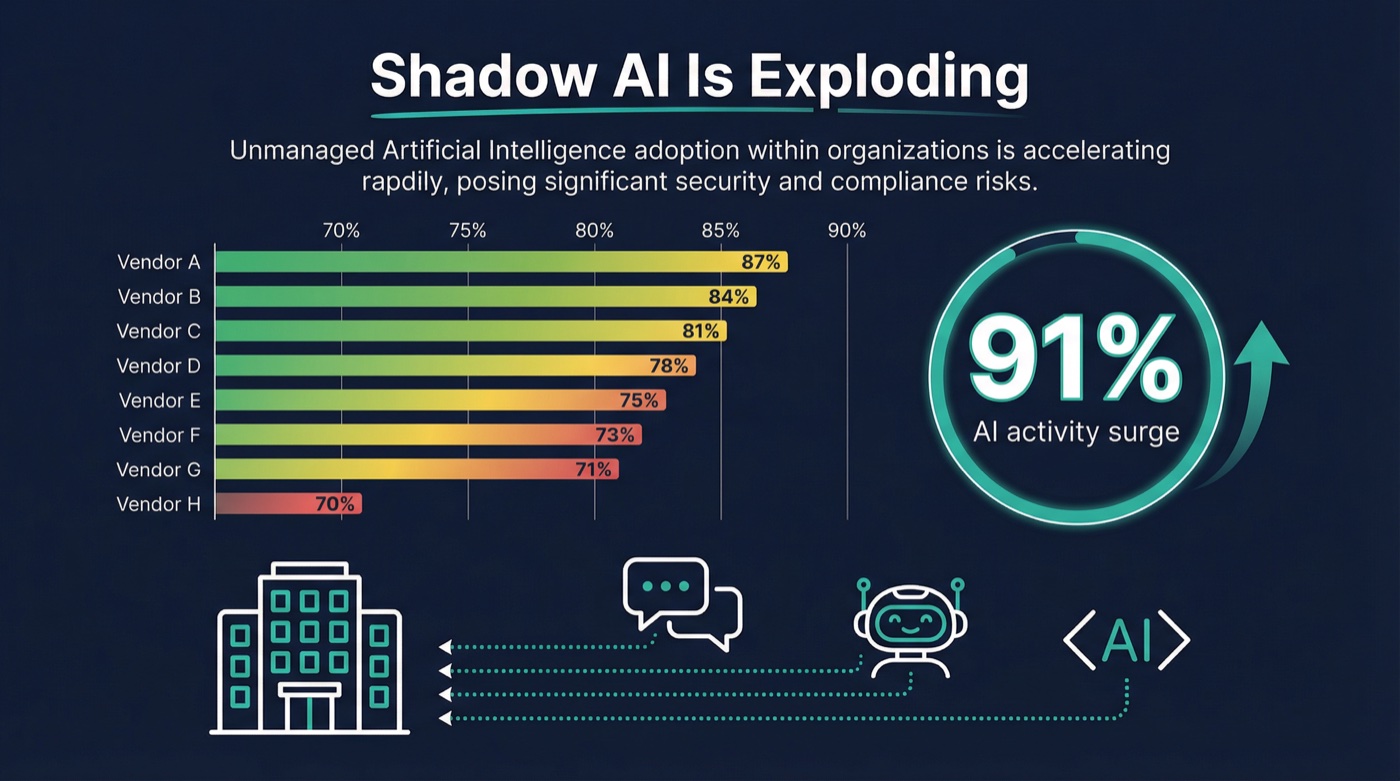
The numbers are staggering and they are getting worse every quarter. Zscaler's ThreatLabz 2026 AI Security Report, analyzing 989 billion AI/ML transactions across 9,000 organizations, found a 91% year-over-year surge in enterprise AI activity. Data transfers to AI tools hit 18,000 terabytes in 2025 alone, a 93% increase.
But here is the part that should alarm every CISO: despite these numbers, enterprises still blocked only 39% of AI access attempts. The other 61% flowed freely, much of it through tools that IT never approved and often does not even know exist.
This is shadow AI. And it is not a theoretical risk. It is the single fastest-growing security gap in enterprise IT.
Every major SASE vendor has rushed to announce AI security features in the past six months. Cisco declared an "AI-Aware SASE" era. Palo Alto launched SASE 4.0 with AI agent discovery. Cato acquired Aim Security for $350 million. Fortinet shipped FortiOS 8.0 with a dedicated shadow AI dashboard. The marketing is loud. But does any of it actually work?
We tested 8 SASE vendors across 28 specific capability checks. The results reveal a market that is further along than you might expect on basic detection, but still dangerously immature on the threats that matter most: agentic AI, streaming protocol inspection, and mobile AI coverage.